Identify, monitor, & assess resources and vulnerabilities

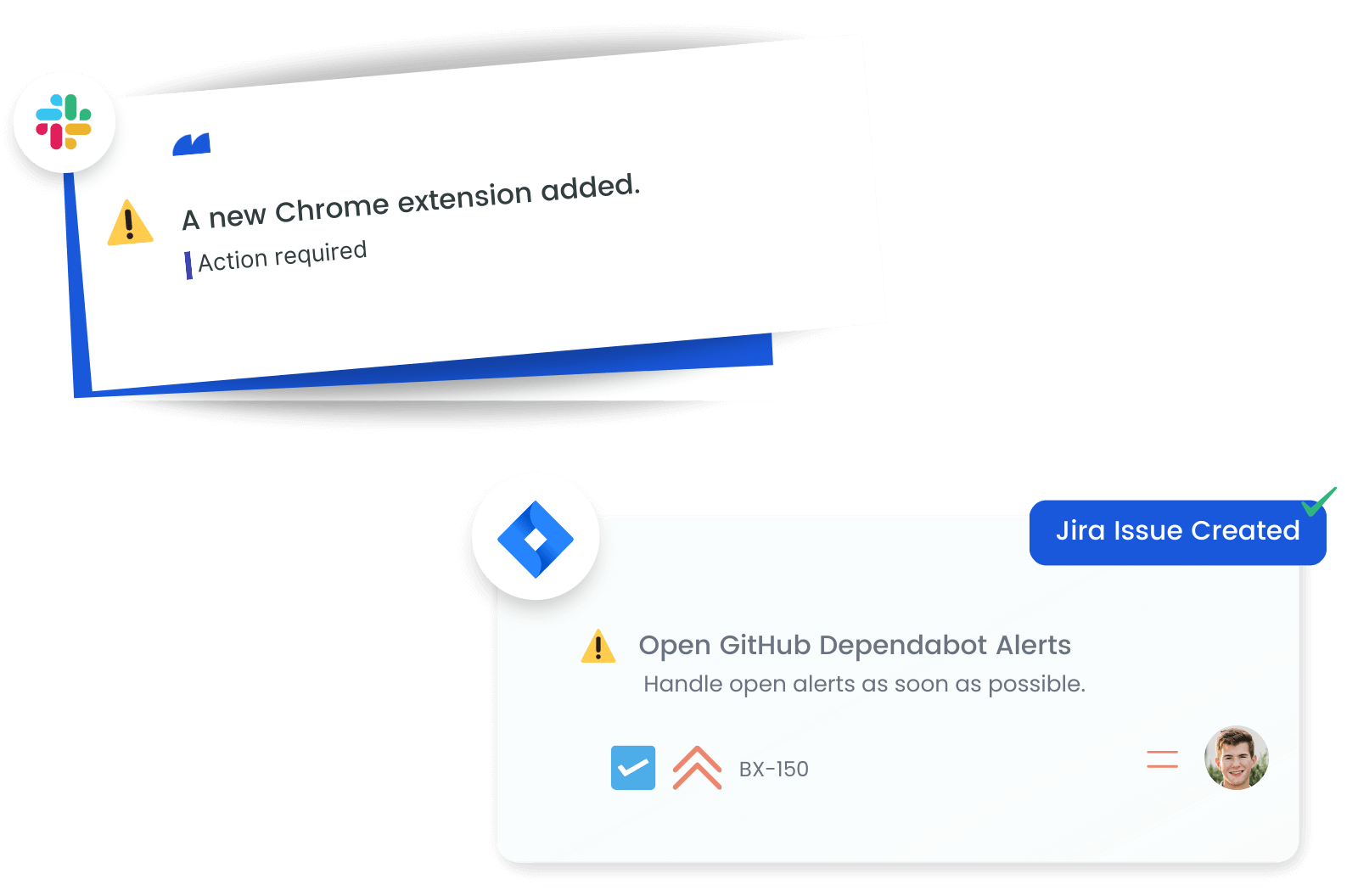
Monitor Browser Extension Security
Track and manage browser extensions across your organization's devices using Microsoft Defender data. Monitoring extension details like ID, version, and risk level helps ensure they comply with your security policies, reducing the risk of extension-related vulnerabilities.
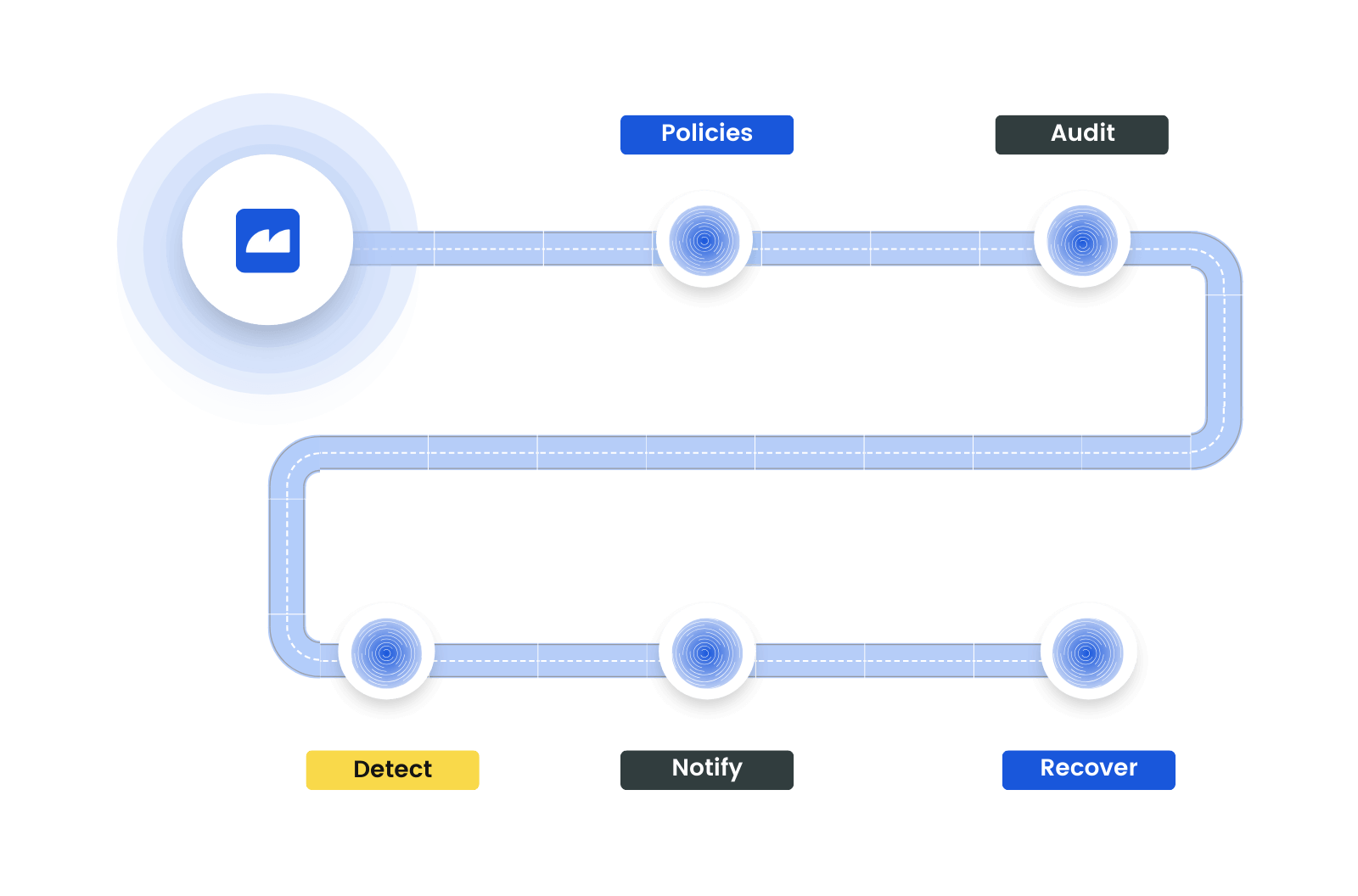
Automate Security Policies
Utilize Microsoft Defender data to implement and enforce security policies. Assess certificate trustworthiness, manage browser extension risks, and analyze software vulnerabilities to ensure your security measures align with organizational standards and best practices.
Get Notifies of Vulnerabilities and Changes in Real-Time
Set up real-time alerts based on Microsoft Defender data to stay ahead of potential security threats. Receive notifications for new vulnerabilities, software risks, or policy deviations, ensuring quick and proactive responses to maintain a secure environment.
Prioritize and Mitigate Threats
Prioritize and address security risks identified by Microsoft Defender. Analyze recommendations, vulnerabilities, and software assessments to develop a targeted approach for risk mitigation, strengthening your organization's defense against cyber threats.
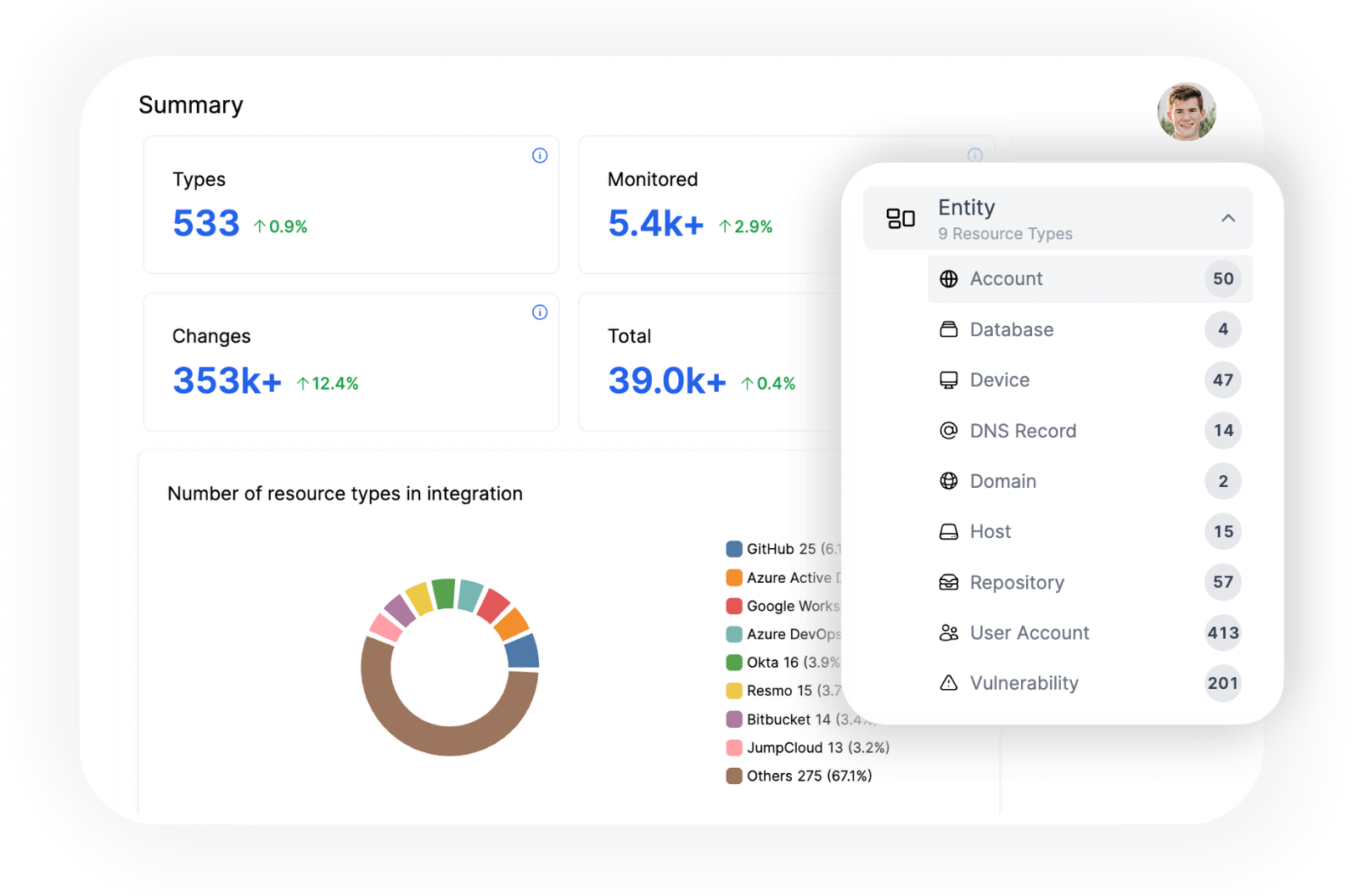
Explore all resources from a unified view.
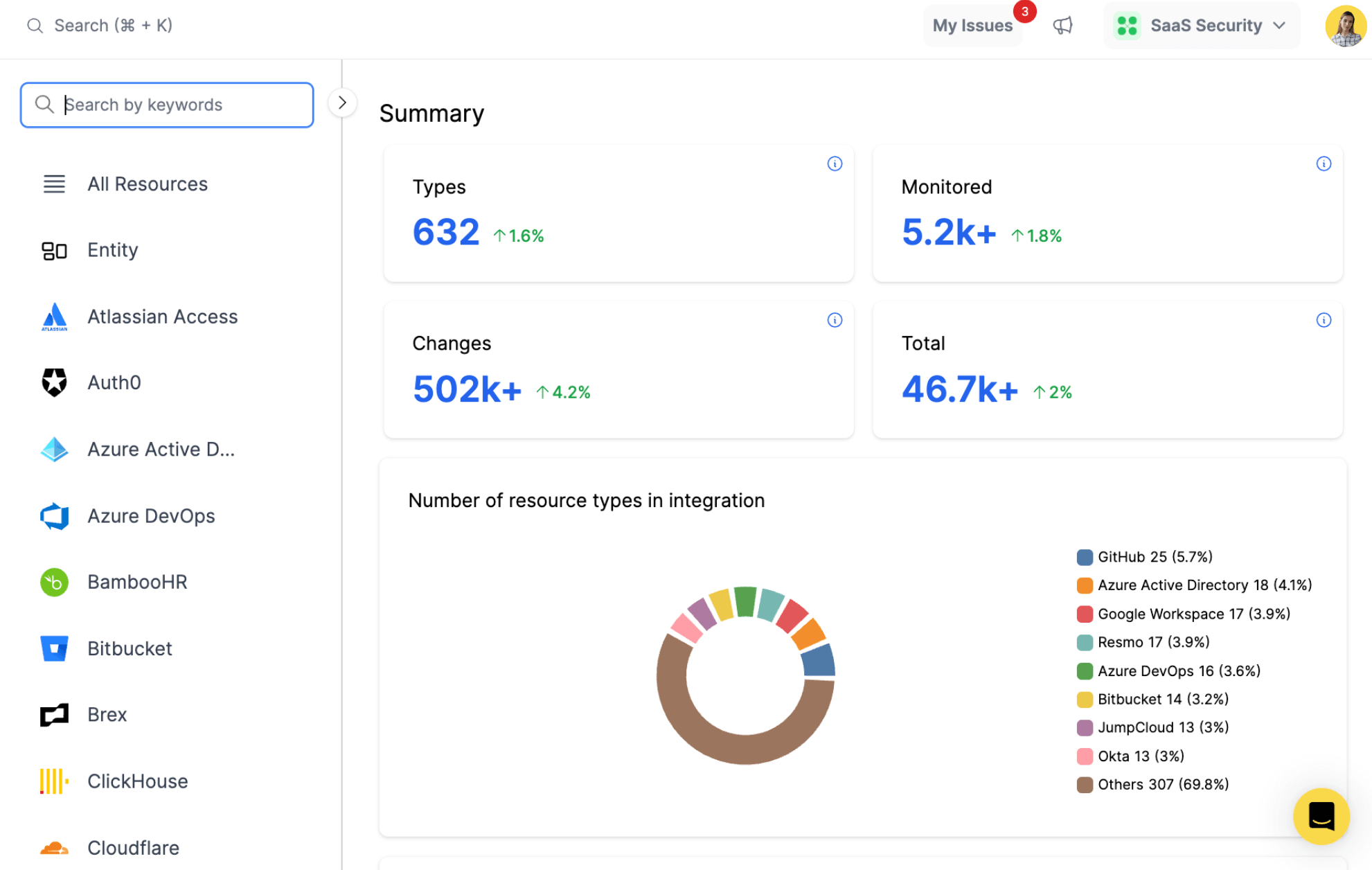
resources
All key resources. Collected in near real time.
- Browser Extension
- Certificate Assessment
- Recommendation
- Software
- Vulnerability
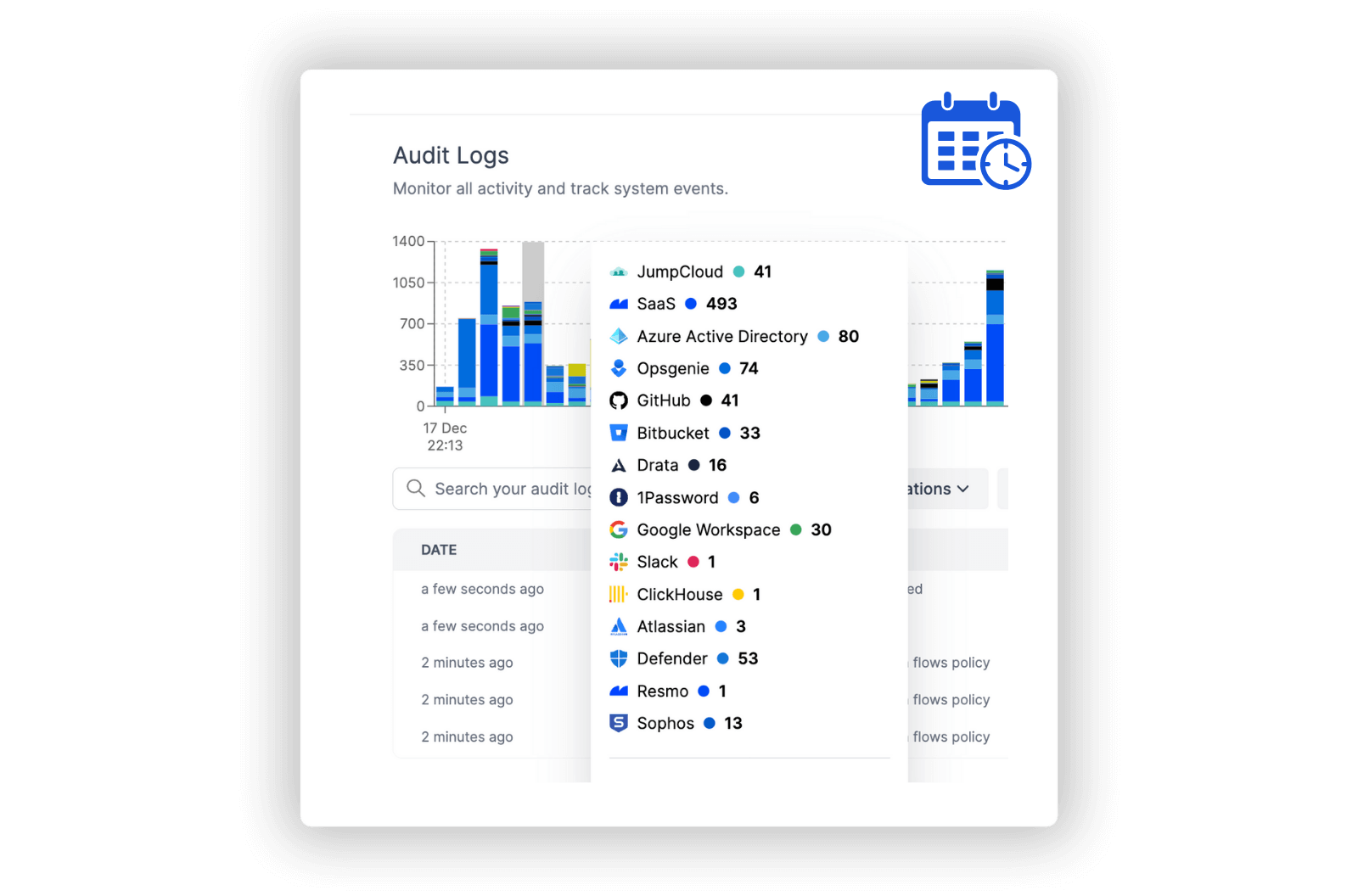
Microsoft Defender Integration with Resmo
Microsoft Defender is a comprehensive, advanced, and integrated security solution from Microsoft. It provides protection against a wide array of security threats, including malware, viruses, and phishing attacks, and offers continuous, real-time security updates across various platforms.
With Resmo's integration with Microsoft Defender, you obtain a thorough understanding of your cybersecurity ecosystem. By offering insights into browser extensions, certificate assessments, software assets, and vulnerabilities, this integration empowers you to optimize your system's security posture and take proactive, informed measures to mitigate risks.
Key features:
- Monitor and control browser extensions to ensure compliance with Microsoft Defender's organizational policies.
- Evaluate the trustworthiness of certificates within your Microsoft Defender environment.
- Prioritize and remediate vulnerabilities and weaknesses based on Microsoft Defender's security recommendations.
- Assess the security profile of software assets and enact necessary measures to reduce risks in Microsoft Defender.
- Spot and address critical software vulnerabilities to minimize the chance of exploitation in Microsoft Defender.
Secure your growth. Know what is happening on SaaS and Cloud.









